Analyze Microsoft Office documents for
security, malware, and forensics.
DOCX XLSX PPTX and more...
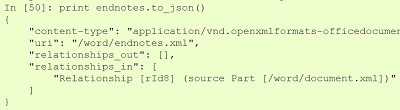
OfficeDissector is a Python toolkit to analyze Microsoft Office Open XML (OOXML) files and documents—the format used by Microsoft Word, Excel, and PowerPoint. It is the most powerful tool for security analysis of Office documents.
import officedissector doc = officedissector.doc.Document('word.docx') mp = doc.main_part() print mp.content_type() # application/vnd.openxmlformats-officedocument.wordprocessingml.document.main+xml